How Can Fake Ids Scan
2024-04-30 2024-04-30 23:14How Can Fake Ids Scan
How Can Fake Ids Scan
Fake SSN Card
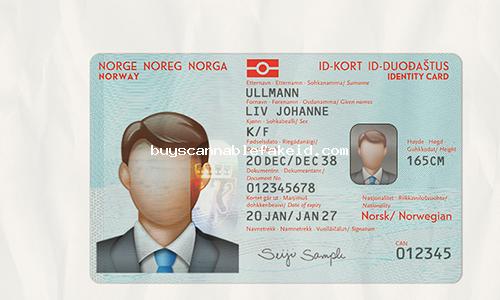
Norway Id Card Fake Scannable
Portugal Id Card Fake Scannable
Slovakia Id Card Fake Scannable
Fake IDs have been a popular means for individuals, especially young adults, to gain access to venues such as bars and clubs where they are legally not allowed to enter. While the use of fake IDs may seem harmless to some, it is important to understand the potential consequences and risks involved in using them. One common concern when it comes to fake IDs is their ability to scan and pass inspection during the ID verification process.
The advancement of technology has made it easier for counterfeiters to create fake IDs that look nearly identical to genuine ones. In some cases, fake IDs may even have barcodes, magnetic stripes, or RFID chips embedded in them to mimic the functionality of real IDs. This raises the question of how fake IDs can scan and potentially fool scanners and ID verification systems.
One of the most common methods used by counterfeiters to make fake IDs scan is by using high-quality printers and scanners to replicate the physical features of real IDs. This includes copying the holograms, UV watermarks, and other security features that are present on genuine IDs. By accurately replicating these features, fake IDs can pass visual inspection and may also be able to fool simple barcode scanners that rely solely on the information displayed on the front of the ID.
However, more sophisticated ID verification systems have been developed to combat the use of fake IDs. These systems are designed to not only scan the information displayed on the front of the ID but also to read data from the barcode, magnetic stripe, or RFID chip embedded in the ID. This data is then cross-referenced with a database of authentic IDs to determine if the ID is genuine or fake.
To make fake IDs scan and pass these more advanced ID verification systems, counterfeiters have also stepped up their game by creating fake IDs with encoded data that matches that of real IDs. This involves using specialized equipment to program the barcode, magnetic stripe, or RFID chip with information that matches the format and encoding standards of authentic IDs. By doing so, fake IDs can pass through scanners and verification systems without raising any red flags.
Another method that counterfeiters use to make fake IDs scan is by exploiting vulnerabilities in the software or hardware of ID scanners. This can involve hacking into the scanner’s system to bypass security checks or to manipulate the data being scanned. In some cases, counterfeiters may even use counterfeit or stolen authentication keys to give their fake IDs the appearance of being genuine.
Despite the efforts of counterfeiters to make fake IDs scan and pass verification systems, there are still ways for businesses and establishments to detect and prevent the use of fake IDs. One common method is to train staff to look for subtle signs of a fake ID, such as misspellings, inconsistencies in the information displayed, or poor-quality printing. Another approach is to use multi-factor authentication methods, such as asking for a second form of ID or using biometric verification, to verify the identity of the individual presenting the ID.
In conclusion, while fake IDs may be able to scan and pass through some ID verification systems, it is important for businesses and establishments to remain vigilant and employ best practices to detect and prevent the use of fake IDs. By staying informed about the latest techniques used by counterfeiters and implementing robust security measures, businesses can protect themselves from potential risks and liabilities associated with the use of fake IDs.